Network
Devices: Repeaters, bridges, gateways, routers:
Repeater:
A repeater is an electronic device that receives a signal and retransmits it at
a higher
level or higher power, or onto the other side of an obstruction, so that the
signal can cover
longer distances without degradation. In most twisted pair Ethernet
configurations, repeaters
are required for cable runs longer than 100 meters.
Bridges:
A network bridge connects multiple network segments at the data link layer of
the OSI
model. Bridges do not promiscuously copy traffic to all ports, as a hub do, but
learns which
MAC addresses are reachable through specific ports. Once the bridge associates
a port
and an address, it will send traffic for that address only to that port.
Bridges do send broadcasts
to all ports except the one on which the broadcast was received. Bridges learn the
association of ports and addresses by examining the source address of frames
that it sees
on various ports. Once a frame arrives through a port, its source address is
stored and the
bridge assumes that MAC address is associated with that port. The first time
that a previously
unknown destination address is seen, the bridge will forward the frame to all ports
other than the one on which the frame arrived.
Gateway:
Gateways work on all seven OSI layers. The main job of a gateway is to convert protocols
among communications networks. A router by itself transfers, accepts and relays packets
only across networks using similar protocols. A gateway on the other hand can accept
a packet formatted for one protocol (e.g. AppleTalk) and convert it to a packet formatted
for another protocol (e.g. TCP/IP) before forwarding it. A gateway can be implemented
in hardware, software or both, but they are usually implemented by software installed
within a router. A gateway must understand the protocols used by each network linked
into the router. Gateways are slower than bridges, switches and (non-gateway) routers. A gateway is a network point that acts
as an entrance to another network. On the Internet,
a node or stopping point can be either a gateway node or a host (end-point)
node. Both
the computers of Internet users and the computers that serve pages to users are
host nodes,
while the nodes that connect the networks in between are gateways. For example, the
computers that control traffic between company networks or the computers used
by internet
service providers (ISPs) to connect users to the internet are gateway nodes.
Router:
A router is a key device in the internet communication and wan communication system.
A router has software called routing table and the source and destination
addresses are
stored in the routing table. Routers are networking devices that forward data
packets between
networks using headers and forwarding tables to determine the best path to forward
the packets. Routers work at the network layer of the TCP/IP model or layer 3
of the
OSI model. Routers also provide interconnectivity between like and unlike
media. This is
accomplished by examining the Header of a data packet, and making a decision on
the next
hop to which it should be sent. They use preconfigured static routes, status of
their hardware
interfaces, and routing protocols to select the best route between any two subnets.
A router is connected to at least two networks, commonly two LANs or WANs or a LAN
and its ISP's network. Some DSL and cable modems, for home and office use, have been
integrated with routers to allow multiple home/office computers to access the
Internet through
the same connection. Many of these new devices also consist of wireless access points
(waps) or wireless routers to allow for IEEE 802.11b/g wireless enabled devices
to connect
to the network without the need for a cabled connection.
The
Network Layer
Maintaining
the quality of service requested by the transport layer.
The
network layer performs network routing functions, and might also perform fragmentation and
reassembly, and report delivery errors.
Design
Issues:
IPv4
Addresses:
Each
device on a network must be uniquely defined. At the Network layer, the packets of the communication
need to be identified with the source and destination addresses of the two end systems.
With IPv4, this means that each packet has a 32-bit source address and a 32-bit destination
address in the Layer 3 header. These addresses are used in the data network as
binary patterns.
Inside the devices, digital logic is applied for their interpretation. For us
in the human network,
a string of 32 bits is difficult to interpret and even more difficult to
remember.
Therefore,
we represent IPv4 addresses using dotted decimal format.
Network
Layer Addressing:
Dotted
Decimal
Binary
patterns representing IPv4 addresses are expressed as dotted decimals by separating each byte
of the binary pattern, called an octet, with a dot. It is called an octet
because each decimal number represents one byte or 8 bits.
For
example, the address: 10101100000100000000010000010100
is
expressed in dotted decimal as: 172.16.4.20
Keep
in mind that devices use binary logic. The dotted decimal format is used to
make it easier for
people to use and remember addresses.
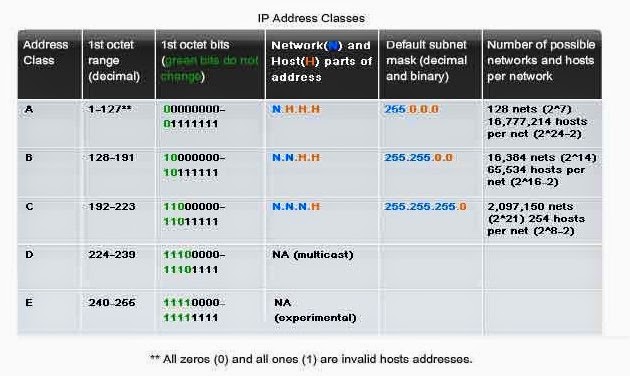
Class full Addressing
Routing
concepts (Forwarding Function, Filtering Function):
Filtering: A
filter is installed on the forwarding plane. This filter counts and applies the
actions to the categories
of traffic Because the filter is enforced in the forwarding plane, it prevents
traffic from consuming
bandwidth on the interface that connects the forwarding plane to the router
control plane. The counters
serve as an important forensic tool for the analysis of potential attacks, and
as an invaluable debugging
and troubleshooting aid. By adjusting the granularity and order of the filters,
more granular forensics can be performed (i.e., create a filter that matches only traffic allowed from a group of IP addresses
for a given protocol followed by a filter that denies all traffic for that
protocol). This would allow
for counters to be monitored for the allowed protocol filter, as well as any
traffic matching the specific
protocol that didn't originate from the explicitly allowed hosts.
Forwarding:
In addition to the filters, rate limiters for certain classes of traffic are
also installed in the forwarding plane.
These rate limiters help further control the traffic that will reach the router
control plane
for each filtered class as well as all traffic not matching an explicit class.
The actual rates selected for
various classes are network deployment specific; analysis of the rates required
for stability should be done
periodically. It is important to note that the most significant factor to
consider regarding the traffic profile
going to the router control plane is the packets per second (pps) rate.
Therefore, careful consideration
must be given to determine the maximum pps rate that could be generated from a
given set of
packet size and bandwidth usage scenarios.
Routing:
is the act of moving information across an internetwork from a source to a
destination.
Along
the way, at least one intermediate node typically is encountered.
Static
Versus Dynamic:
Static
routing algorithms are hardly algorithms at all, but
are table mappings established by the network
administrator before the beginning of routing. These mappings do not change
unless the network
administrator alters them. Algorithms that use static routes are simple to
design and work
well in environments where network traffic is relatively predictable and where
network design
is relatively simple.
Because
static routing systems cannot react to network changes, they generally are
considered unsuitable
for today's large, constantly changing networks. Most of the dominant routing algorithms
today are dynamic routing algorithms, which adjust to changing network circumstances
by analyzing incoming routing update messages. If the message indicates that a network
change has occurred, the routing software recalculates routes and sends out new
routing update
messages. These messages permeate the network, stimulating routers to rerun
their algorithms
and change their routing tables accordingly.
Dynamic
routing algorithms can be supplemented with static
routes where appropriate. A router of
last resort (a router to which all unroutable packets are sent), for example, can
be designated to
act as a repository for all unroutable packets, ensuring that all messages are
at least handled in some
way
Hierarchical
Routing :In a hierarchical routing system, some
routers form what amounts to a
routing
backbone. Packets from nonbackbone routers travel to the backbone routers,
where they
are
sent through the backbone until they reach the general area of the destination.
At this point,
they
travel from the last backbone router through one or more nonbackbone routers to
the final
destination.
Routing
systems often designate logical groups of nodes, called domains, autonomous
systems,
or
areas. In hierarchical systems, some routers in a domain can communicate with
routers in
other
domains, while others can communicate only with routers within their domain. In
very
large
networks, additional hierarchical levels may exist, with routers at the highest
hierarchical
level forming the routing backbone.
Routing:
is the act of moving information across an internetwork from a source to a
destination.
Along
the way, at least one intermediate node typically is encountered.
Static
Versus Dynamic:
Static
routing algorithms are hardly algorithms at all, but
are table mappings established by the network
administrator before the beginning of routing. These mappings do not change
unless the network
administrator alters them. Algorithms that use static routes are simple to
design and work
well in environments where network traffic is relatively predictable and where
network design
is relatively simple.
Because
static routing systems cannot react to network changes, they generally are
considered unsuitable
for today's large, constantly changing networks. Most of the dominant routing algorithms
today are dynamic routing algorithms, which adjust to changing network circumstances
by analyzing incoming routing update messages. If the message indicates that a network
change has occurred, the routing software recalculates routes and sends out new
routing update
messages. These messages permeate the network, stimulating routers to rerun
their algorithms
and change their routing tables accordingly.
Dynamic
routing algorithms can be supplemented with static
routes where appropriate. A router of
last resort (a router to which all unroutable packets are sent), for example, can
be designated to
act as a repository for all unroutable packets, ensuring that all messages are
at least handled in some
way.
Hierarchical
Routing :In a hierarchical routing system, some
routers form what amounts to a routing
backbone. Packets from nonbackbone routers travel to the backbone routers,
where they are
sent through the backbone until they reach the general area of the destination.
At this point, they
travel from the last backbone router through one or more nonbackbone routers to
the final destination.
Routing
systems often designate logical groups of nodes, called domains, autonomous
systems, or
areas. In hierarchical systems, some routers in a domain can communicate with
routers in other
domains, while others can communicate only with routers within their domain. In
very large
networks, additional hierarchical levels may exist, with routers at the highest
hierarchical level forming the routing backbone.
The
primary advantage of hierarchical routing is that it mimics the organization of
most companies
and therefore supports their traffic patterns well. Most network communication occurs
within small company groups (domains). Because intradomain routers need to know
only about
other routers within their domain, their routing algorithms can be simplified,
and, depending
on the routing algorithm being used, routing update traffic can be reduced accordingly.
Distributed
routing:
The
key to a distributed routing is to apply a decomposition of problem. For
solving the problem, we
propose to apply the common approach of using any simple routing protocol.
Distance
Vector Protocol, Link State protocol:
Link-state
algorithms (also known as shortest path first algorithms) flood routing
information to all
nodes in the internetwork. Each router, however, sends only the portion of the
routing table that
describes the state of its own links. In link-state algorithms, each router
builds a picture of the
entire network in its routing tables. Distance vector algorithms (also known as
Bellman-Ford algorithms)
call for each router to send all or some portion of its routing table, but only
to its neighbors.
In essence, link-state algorithms send small updates everywhere, while distance vector
algorithms send larger updates only to neighboring routers. Distance vector
algorithms
know
only about their neighbors.
Because
they converge more quickly, link-state algorithms are somewhat less prone to
routing loops
than distance vector algorithms. On the other hand, link-state algorithms
require more CPU power
and memory than distance vector algorithms. Link-state algorithms, therefore,
can be more
expensive to implement and support. Link-state protocols are generally more
scalable than distance vector protocols.
No comments:
Post a Comment